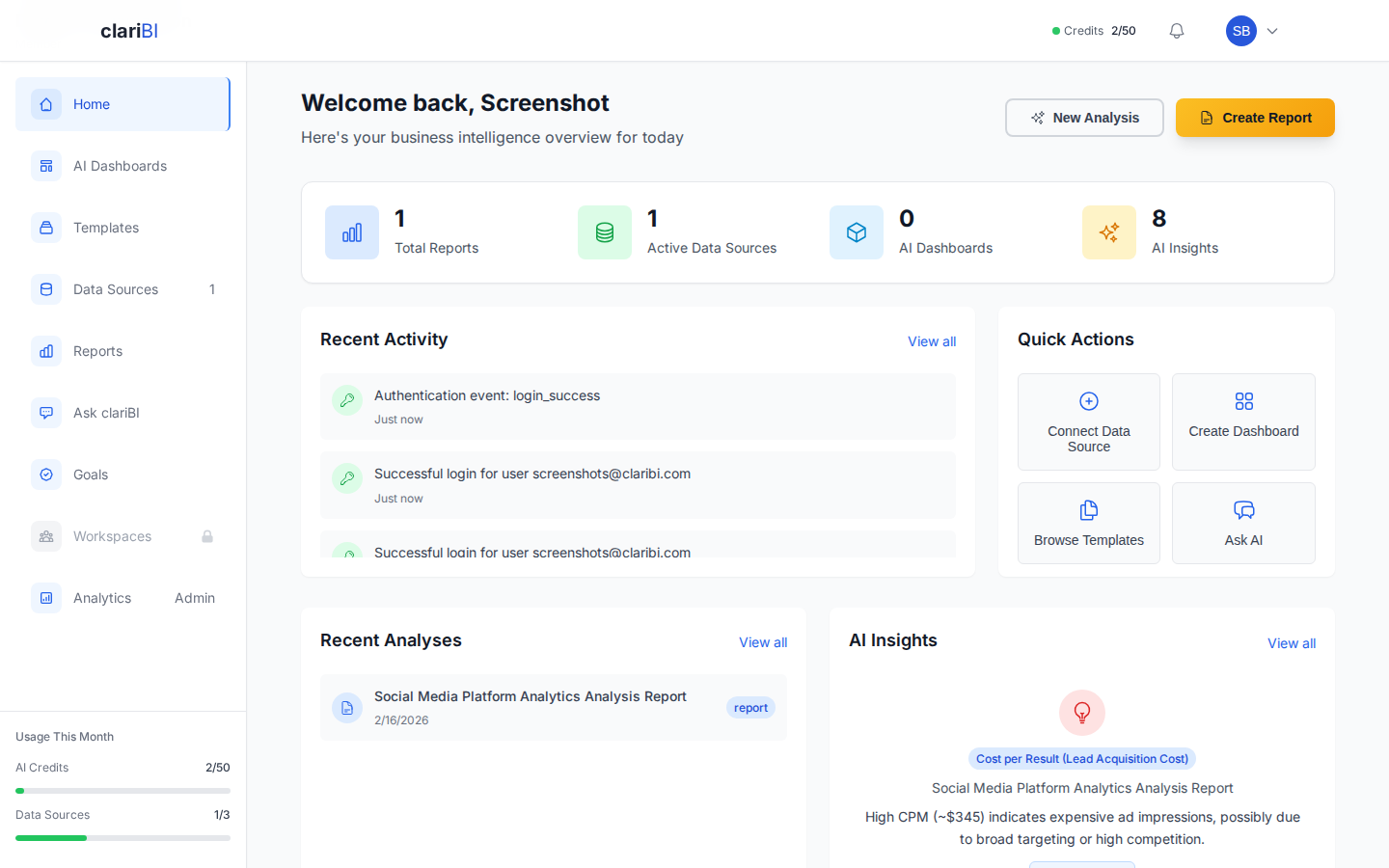
Overview
Session settings control how long you stay logged in, when you are notified about new logins, and how you can review past login activity. These settings help you balance convenience with security.
Access session settings from Settings > Security > Sessions.
Session Timeouts
What Is a Session Timeout?
A session timeout automatically logs you out after a period of inactivity. This protects your account if you walk away from your computer without logging out.
Configuring Timeout Duration
- Go to Settings > Security > Sessions.
- Find the Session Timeout section.
- Choose a timeout duration:
- 15 minutes -- High security, recommended for shared computers
- 30 minutes -- Balanced security (default)
- 1 hour -- Convenient for frequent use
- 4 hours -- Low security, for trusted devices
- 8 hours -- Minimal timeout, full workday
- Click Save.
The timeout applies to browser inactivity. As long as you are actively using clariBI (clicking, scrolling, typing), the session remains active. The timer resets with each interaction.
Organization-Wide Timeout Policies
Organization Owners can enforce a maximum session timeout for all members:
- Go to Settings > Organization > Security Policies.
- Set the Maximum Session Duration.
- Individual members cannot set a timeout longer than this limit.
For example, if the organization maximum is 1 hour, a member who sets their timeout to 4 hours will still be logged out after 1 hour.
Login Notifications
How They Work
When enabled, clariBI sends you a notification each time someone logs into your account. This helps you detect unauthorized access quickly.
Enabling Login Notifications
- Go to Settings > Security > Sessions.
- Toggle Login Notifications to on.
- Choose your notification channels:
- In-app notification -- A bell icon alert in clariBI
- Email notification -- An email sent to your registered address
- Click Save.
What Notifications Include
Each login notification contains:
- Date and time of the login
- IP address
- Approximate location (city, country)
- Browser and operating system
- Whether MFA was used
If you receive a notification for a login you did not make, change your password immediately and review your active sessions.
Login History
Viewing Your Login History
- Go to Settings > Security > Sessions.
- Scroll to the Login History section.
The login history shows your last 50 login events, including:
| Field | Description |
|---|---|
| Date & Time | When the login occurred |
| IP Address | The IP address used |
| Location | Approximate city and country |
| Device | Browser and OS (e.g., "Chrome on macOS") |
| Status | Success, Failed, or MFA Required |
Identifying Suspicious Activity
Look for:
- Unfamiliar locations -- Logins from countries or cities you have not visited
- Unusual times -- Logins at hours when you are normally not working
- Failed attempts -- Multiple failed login attempts may indicate a brute-force attack
- Unknown devices -- Browsers or operating systems you do not use
If you spot suspicious activity, take these steps:
- Change your password immediately.
- Enable MFA if not already active (see MFA Setup: TOTP Authenticator App and Backup Codes).
- Review and terminate active sessions (see below).
- Notify your organization's Administrator.
Managing Active Sessions
Viewing Active Sessions
The Active Sessions panel shows all devices currently logged into your account:
- Device name and browser
- IP address and location
- When the session started
- Last activity timestamp
Terminating Sessions
To log out a specific session:
- Find the session in the Active Sessions list.
- Click Terminate next to it.
To log out all sessions except your current one:
- Click Terminate All Other Sessions at the top of the panel.
- Confirm the action.
This is useful if you suspect unauthorized access or if you logged in on a shared computer and forgot to log out.
Best Practices
- Use 30-minute timeouts on work computers and shorter timeouts on shared devices.
- Enable both notification channels. In-app notifications are fast, but email provides a record you can check later.
- Review login history monthly. A quick scan helps catch issues early.
- Terminate sessions you do not recognize. It is better to be cautious -- terminating a legitimate session just means you need to log in again.
- Combine with MFA. Session settings and MFA work together. Even if a session is hijacked, MFA prevents new logins.